Trunking protocols
We saw in a previous article the advantages of VLANs. In this article we’ll see how the communication between two hosts that are in the same VLAN but not plugged on the same Switch works.
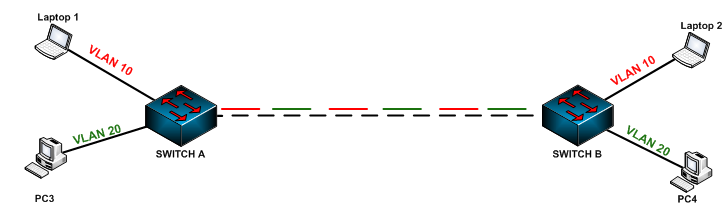
Imagine that we have the following architecture:
Note that Laptop 1 and Laptop 2 are in the same VLAN (VLAN 10) but not connected to the same Switch, Same thing for PC3 and PC4. How can Laptop 1 communicate with Laptop 2?
When Laptop 1 tries to communicate with his friend Laptop 2, he will send an ARP request frame to SWITCH A. We know that ARP frames are sent using broadcast, this means that SWITCH A will broadcast the ARP request on the ports that are in VLAN 10 except the port where it receives the frame.
Are you following me so far?! The problem comes mainly from connection between SWITCH A and SWITCH B. So why we have this problem?
In fact, when you start a Switch, all ports are affected by default to a default VLAN which is VLAN1.
How about affecting ports connecting SWITCH A and SWITCH B to VLAN 10? It is one solution to make LAPTOP 1 and LAPTOP2 communicate with each other, but PC3 and PC4 will never succeed to communicate.
Do you have any idea to solve this problem? Is there any way to make the connection between SWITCH A and SWITCH B supports traffic of all VLANs? Yes there is one, it is the Trunking protocol.
Trunking means that between SWITCH A and SWITCH B, we will create a trunk, which is an interface that carries multiple VLANs.
Here how it will looks like:
In fact, there are two trunking protocols:
- IEEE 802.1Q: OpenStandard which is suppprted by many switches.
- CISCO ISL (Inter-Switch Link): Which is an old trunking protocol and Cisco proprietary.
In 802.1Q, the frame is tagged:
You can see that the frame is tagged, and in the frame we have the VLAN Identifier. This field is used by SWITHC B when he receives a frame from SWITCH A to identify to which VLAN the frame belongs.
The Cisco ISL protocol is a bit different from 802.1Q, let’s see this:
You can see that in the ISL protocol, the frame is encapsulated by adding an ISL header and FCS. In the ISL header, we’ll find our VLAN identifier.
So to summarize this part, note the main differences between ISL and 802.1Q protocol:
-
In 802.1Q we tag the frame, but in ISL we encapsulate the FRAME.
-
802.1Q is an open Standard, this means that we can enable it on Switches from different vendors, but ISL is Cisco-proprietary, and this means if we want to use, we have to use Cisco equipments.
Last thing before the end of this article is the Native VLAN. Do you know what a native VLAN is?
The Native VLAN is the VLAN that carries the untagged frames. By default this VLAN is the VLAN 1. When a trunk port receives an untagged frame, it associated this frame with the Native VLAN.
This is the end of this article; I hope this was helpful and clear for you. If it was, Don’t hesitate to leave a comment!






It was clear